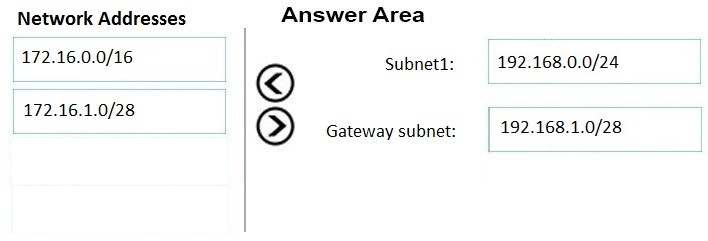
Question 190 of 231 from exam AZ-301: Microsoft Azure Architect Design
Question
DRAG DROP -
You have an on-premises network that uses an IP address space of 172.16.0.0/16.
You plan to deploy 25 virtual machines to a new Azure subscription.
You identify the following technical requirements:
-> All Azure virtual machines must be placed on the same subnet named Subnet1.
-> All the Azure virtual machines must be able to communicate with all on-premises servers.
The servers must be able to communicate between the on-premises network and Azure by using a site-to-site VPN.

You need to recommend a subnet design that meets the technical requirements.
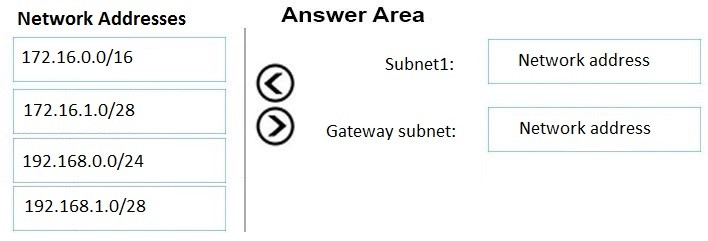
What should you include in the recommendation? To answer, drag the appropriate network addresses to the correct subnets. Each network address may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
Select and Place:
Explanations