Question 63 of 267 from exam AZ-303: Microsoft Azure Architect Technologies
Question
HOTSPOT -
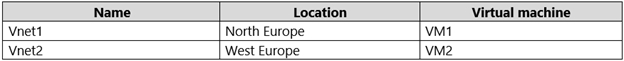
You have an Azure subscription that contains the virtual networks shown in the following table.
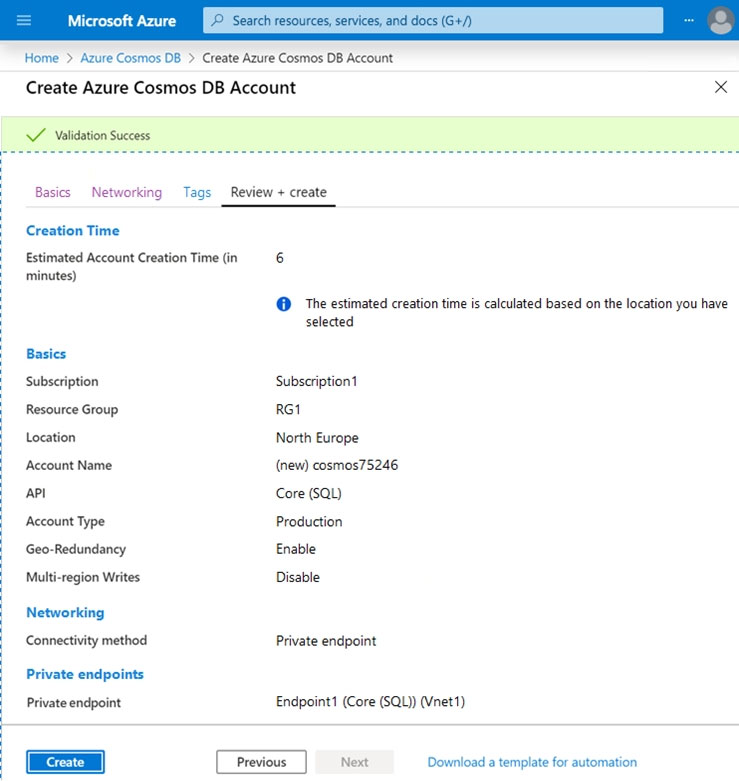
You create an Azure Cosmos DB account as shown in the exhibit. (Click the Exhibit tab.)
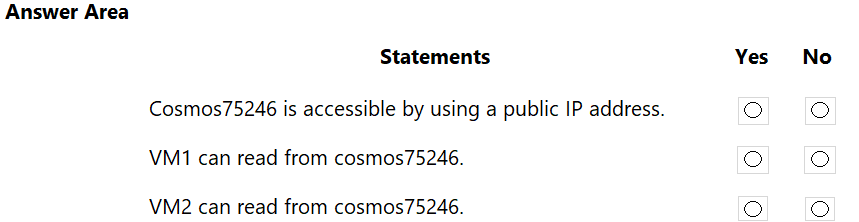
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Hot Area:
Explanations
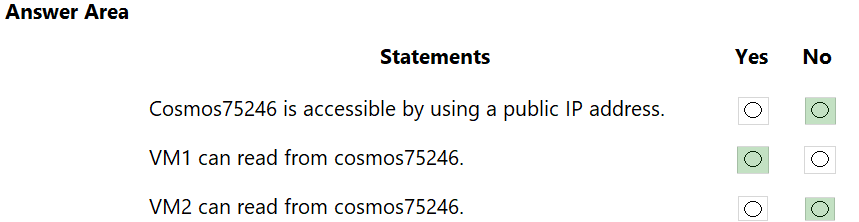
Box 1: No -
Connectivity Method: Private Network
Box 2: Yes -
Private endpoint: Endpoint1 (Core (SQL)) (Vnet1)
VM1 is in Vnet1.
Box 3: No -
VM2 is not in Vnet1.
https://docs.microsoft.com/en-us/azure/private-link/tutorial-private-endpoint-cosmosdb-portal