Question 64 of 267 from exam AZ-303: Microsoft Azure Architect Technologies
Question
HOTSPOT -
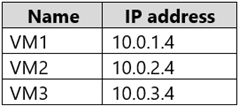
You have an Azure subscription named Subscription1.
Subscription1 contains the virtual machines in the following table.
Subscription1 contains a virtual network named VNet1 that has the subnets in the following table.
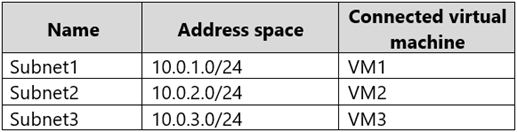
VM3 has a network adapter named NIC3. IP forwarding is enabled on NIC3. Routing is enabled on VM3.
You create a route table named RT1 that contains the routes in the following table.
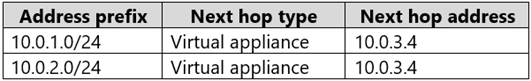
You apply RT1 to Subnet1 and Subnet2.
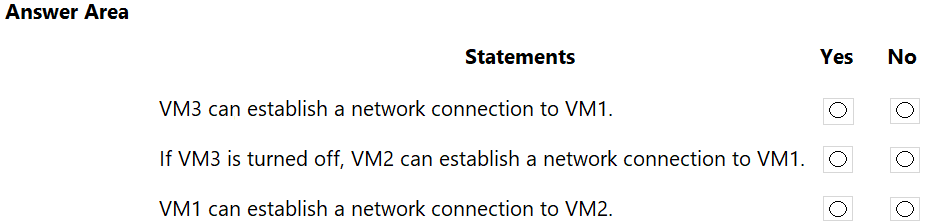
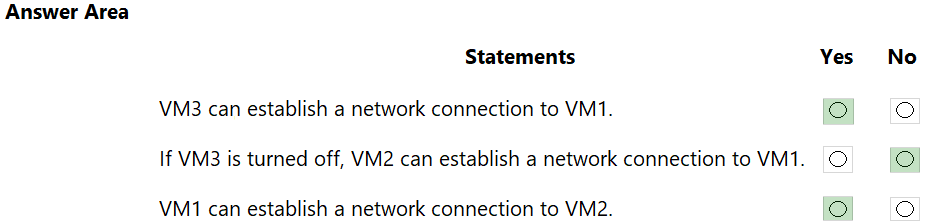
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Hot Area:
Explanations
IP forwarding enables the virtual machine a network interface is attached to:
-> Receive network traffic not destined for one of the IP addresses assigned to any of the IP configurations assigned to the network interface.
-> Send network traffic with a different source IP address than the one assigned to one of a network interface's IP configurations.
The setting must be enabled for every network interface that is attached to the virtual machine that receives traffic that the virtual machine needs to forward. A virtual machine can forward traffic whether it has multiple network interfaces or a single network interface attached to it.
Box 1: Yes -
The routing table allows connections from VM3 to VM1 and VM2. And as IP forwarding is enabled on VM3, VM3 can connect to VM1.
Box 2: No -
VM3, which has IP forwarding, must be turned on, in order for VM2 to connect to VM1.
Box 3: Yes -
The routing table allows connections from VM1 and VM2 to VM3. IP forwarding on VM3 allows VM1 to connect to VM2 via VM3.
https://docs.microsoft.com/en-us/azure/virtual-network/virtual-networks-udr-overview https://www.quora.com/What-is-IP-forwarding