Question 100 of 267 from exam AZ-303: Microsoft Azure Architect Technologies
Question
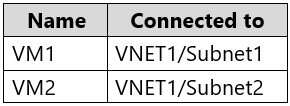
You have an Azure subscription that contains an Azure key vault named KeyVault1 and the virtual machines shown in the following table.
KeyVault1 has an access policy that provides several users with Create Key permissions.
You need to ensure that the users can only register secrets in KeyVault1 from VM1.
What should you do?
Answers
Explanations
Click on the arrows to vote for the correct answer
A. B. C. D.C
You grant data plane access by setting Key Vault access policies for a key vault.
Note 1: Grant our VM's system-assigned managed identity access to the Key Vault.
1. Select Access policies and click Add new.
2. In Configure from template, select Secret Management.
3. Choose Select Principal, and in the search field enter the name of the VM you created earlier. Select the VM in the result list and click Select.
4. Click OK to finishing adding the new access policy, and OK to finish access policy selection.
Note 2: Access to a key vault is controlled through two interfaces: the management plane and the data plane. The management plane is where you manage Key
Vault itself. Operations in this plane include creating and deleting key vaults, retrieving Key Vault properties, and updating access policies. The data plane is where you work with the data stored in a key vault. You can add, delete, and modify keys, secrets, and certificates.
https://docs.microsoft.com/en-us/azure/active-directory/managed-identities-azure-resources/tutorial-windows-vm-access-nonaad https://docs.microsoft.com/en-us/azure/key-vault/general/secure-your-key-vault2