Question 78 of 197 from exam AZ-100: Microsoft Azure Infrastructure and Deployment
Question
You have an Azure subscription named Subscription1. Subscription1 contains a virtual machine named VM1.
You have a computer named Computer1 that runs Windows 10. Computer1 is connected to the Internet.
You add a network interface named Interface1 to VM1 as shown in the exhibit (Click the Exhibit button.)
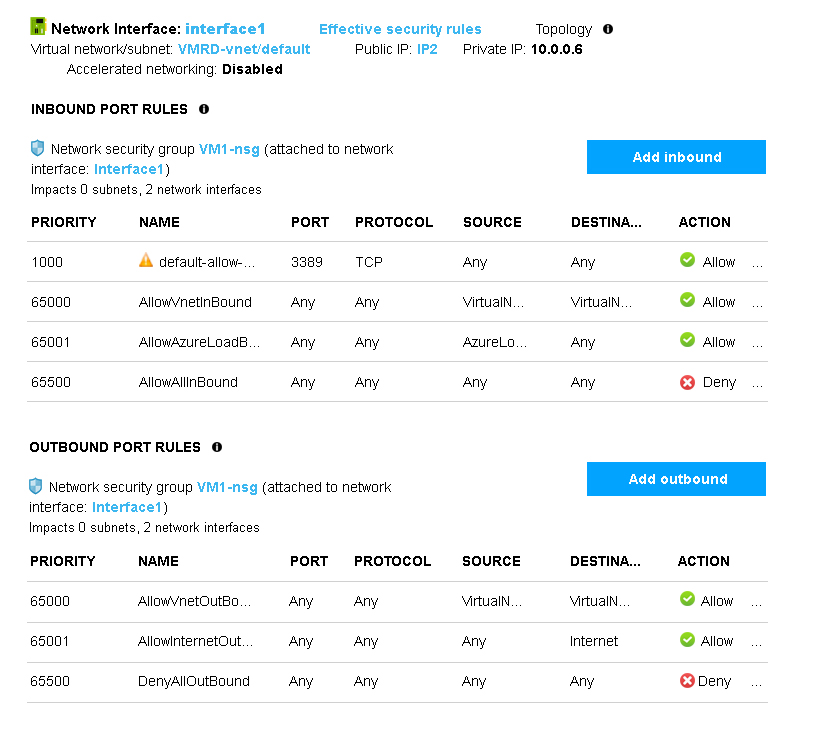
From Computer1, you attempt to connect to VM1 by using Remote Desktop, but the connection fails.
You need to establish a Remote Desktop connection to VM1.
What should you do first?
Answers
Explanations
Click on the arrows to vote for the correct answer
A. B. C. D.A
Incorrect Answers:
B: The network interface has already been added to VM.
C: The Outbound rules are fine.
D: The inbound rules are fine. Port 3389 is used for Remote Desktop.
Note: Rules are processed in priority order, with lower numbers processed before higher numbers, because lower numbers have higher priority. Once traffic matches a rule, processing stops. As a result, any rules that exist with lower priorities (higher numbers) that have the same attributes as rules with higher priorities are not processed.
https://docs.microsoft.com/en-us/azure/virtual-network/security-overview