Question 92 of 197 from exam AZ-100: Microsoft Azure Infrastructure and Deployment
Question
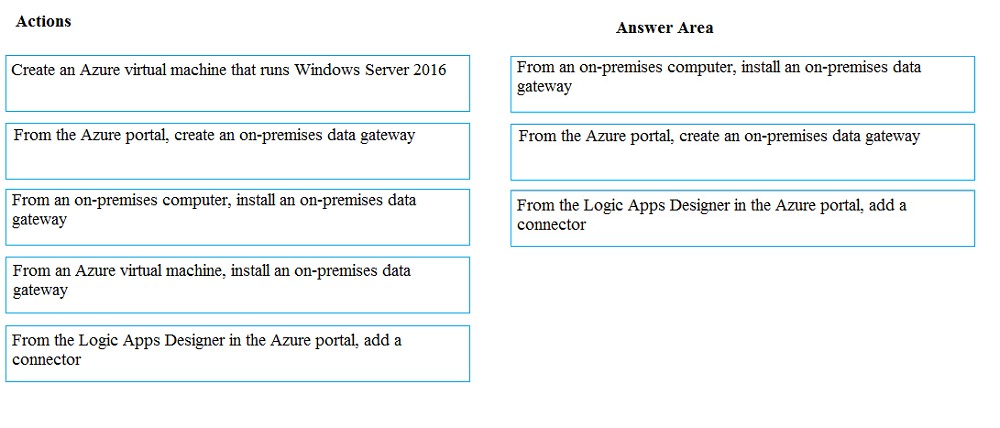
DRAG DROP -
You have on-premises network that includes a Microsoft SQL Server instance named SQL1. You create an Azure Logic App named App1.
You need to ensure that App1 can query a database on SQL1.
Which three actions should you perform in sequence? To answer, move the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
Select and Place: