Question 97 of 197 from exam AZ-100: Microsoft Azure Infrastructure and Deployment
Question
You plan to migrate an on-premises Hyper-V environment to Azure by using Azure Site Recovery. The Hyper-V environment is managed by using Microsoft
System Center Virtual Machine Manager (VMM).
The Hyper-V environment contains the virtual machines in the following table.
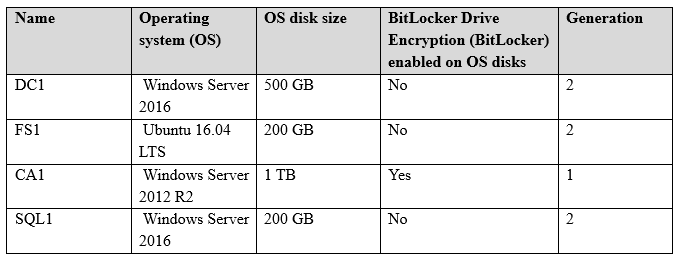
Which virtual machine can be migrated by using Azure Site Recovery?
Answers
Explanations
Click on the arrows to vote for the correct answer
A. B. C. D.D