Question 81 of 197 from exam AZ-100: Microsoft Azure Infrastructure and Deployment
Question
HOTSPOT -
You have an Azure subscription named Subscription1. Subscription1 contains two Azure virtual machines named VM1 and VM2. VM1 and VM2 run Windows
Server 2016.
VM1 is backed up daily by Azure Backup without using the Azure Backup agent.
VM1 is affected by ransomware that encrypts data.
You need to restore the latest backup of VM1.
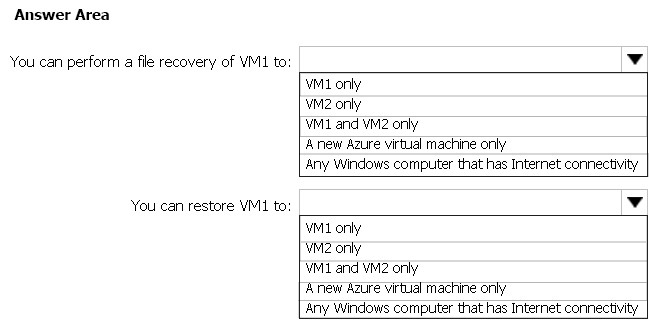
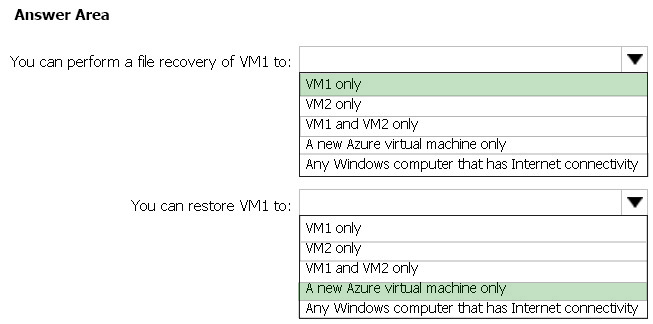
To which location can you restore the backup? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
Explanations
Box 1: VM1 only -
To restore files or folders from the recovery point, go to the virtual machine and choose the desired recovery point.
Box 2: A new Azure virtual machine only
On the Restore configuration blade, you have two choices:
-> Create virtual machine
-> Restore disks
https://docs.microsoft.com/en-us/azure/backup/backup-azure-restore-files-from-vm https://docs.microsoft.com/en-us/azure/backup/backup-azure-arm-restore-vms