Question 99 of 197 from exam AZ-100: Microsoft Azure Infrastructure and Deployment
Question
DRAG DROP -
You create an Azure Migrate project named TestMig in a resource group named test-migration.
You need to discover which on-premises virtual machines to assess for migration.
Which three actions should you perform in sequence? To answer, select the appropriate actions from the list of actions to the answer area and arrange them in the correct order.
Select and Place:
Explanations
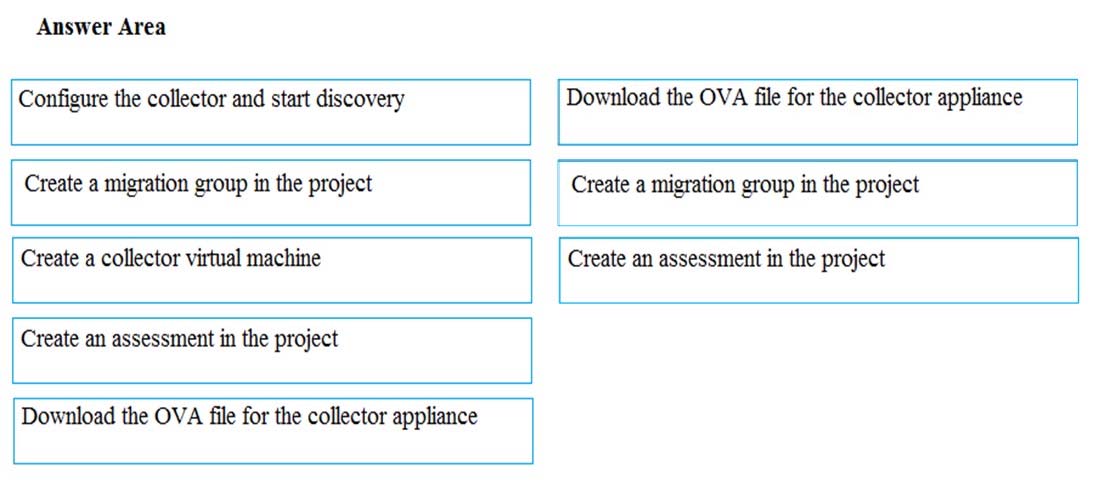
Step 1: Download the OVA file for the collection appliance
Azure Migrate uses an on-premises VM called the collector appliance, to discover information about your on-premises machines. To create the appliance, you download a setup file in Open Virtualization Appliance (.ova) format, and import it as a VM on your on-premises vCenter Server.
Step 2: Create a migration group in the project
For the purposes of assessment, you gather the discovered VMs into groups. For example, you might group VMs that run the same application. For more precise grouping, you can use dependency visualization to view dependencies of a specific machine, or for all machines in a group and refine the group.
Step 3: Create an assessment in the project
After a group is defined, you create an assessment for it.
https://docs.microsoft.com/en-us/azure/migrate/migrate-overview