Question 96 of 197 from exam AZ-100: Microsoft Azure Infrastructure and Deployment
Question
HOTSPOT -
You have an Azure Service Bus.
You create a queue named Queue1. Queue1 is configured as shown in the following exhibit.
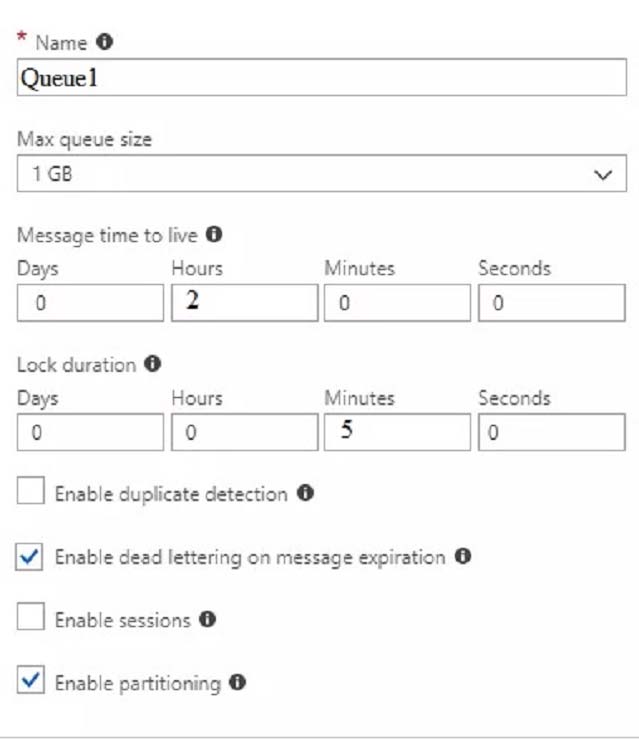
Use the drop-down menus to select the answer choice that completes each statement based on the information presented in the graphic.
NOTE: Each correct selection is worth one point.
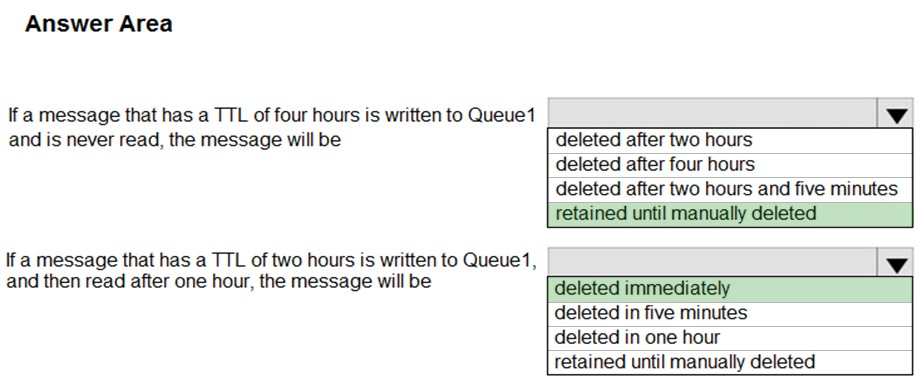
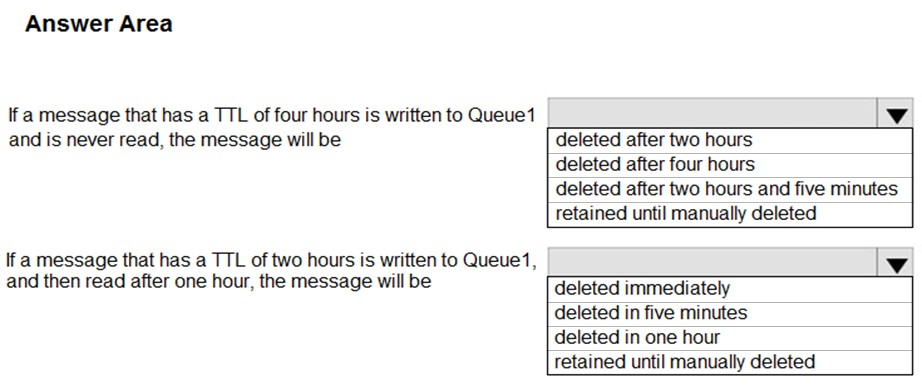
Hot Area:
Explanations